China Cybersecurity Market Growth, Size, Trends, Share, Demand, Revenue and Future Outlook
China Cybersecurity Market Size- By Offering, By Deployment, By End User- Regional Outlook, Competitive Strategies and Segment Forecast to 2033
| Published: Apr-2024 | Report ID: IACT2457 | Pages: 1 - 108 | Formats*: |
| Category : Information & Communications Technology | |||
- July 2022 - To help realize an ambitious goal: unifying threat research across many Palo Alto Networks products, Red Canary, the Managed Detection and Response (MDR) company, has extended its collaboration with Palo Alto Networks. To achieve this goal, Red Canary has partnered with Palo Alto Networks Cortex® MSSP. Palo Alto Networks firewalls are supported by Red Canary MDR's integration with PAN-OS versions nine and higher.
- March 2022: An E+ round of fundraising totaling over 300 million yuan was successfully concluded by Beijing-based ThreatBook, a provider of security threat intelligence. An existing stakeholder, Star Road Ventures, led CDH Investment in completing the transaction.

| Report Metric | Details |
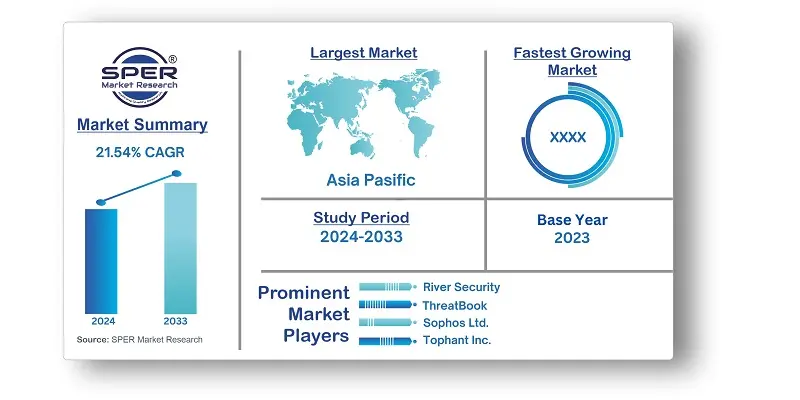
| Market size available for years | 2020-2033 |
| Base year considered | 2023 |
| Forecast period | 2024-2033 |
| Segments covered | By Offering, By Deployment, By End User |
| Regions covered | Eastern, Western, Northern, Southern |
| Companies Covered | Beijing Chaitin Future Technology Co.,Ltd, CoreShield Times, IBM Corporation, IDsManager, iJiami, Palo Alto Networks, QI-ANXIN Technology Group Inc., River Security, ThreatBook, Sophos Ltd., Tophant Inc., Others. |
- Government Agencies
- Financial Institutions
- Healthcare Organizations
- Energy and Utility Companies
- Retail and E-commerce Businesses
- Manufacturing and Industrial Sector
- Educational Institutions
- Telecommunication Companies
- Small and Medium Enterprises (SMEs)
- Legal and Compliance Firms
- Information Technology (IT) Service Providers
| By Offering: |
|
| By Deployment: |
|
| By End User: |
|
- China Cybersecurity Market Size (FY’2024-FY’2033)
- Overview of China Cybersecurity Market
- Segmentation of China Cybersecurity Market By Offering (Security Type, Services)
- Segmentation of China Cybersecurity Market By Deployment (Cloud, On-premise)
- Segmentation of China Cybersecurity Market By End User (BFSI, Healthcare, Manufacturing, Government & Defence, IT and Telecommunication, Others)
- Expansion Analysis of China Cybersecurity Market
- Problems and Obstacles in China Cybersecurity Market
- Competitive Landscape in the China Cybersecurity Market
- Impact of COVID-19 and Demonetization on China Cybersecurity Market
- Details on Current Investment in China Cybersecurity Market
- Competitive Analysis of China Cybersecurity Market
- Prominent Players in the China Cybersecurity Market
- SWOT Analysis of China Cybersecurity Market
- China Cybersecurity Market Future Outlook and Projections (FY’2024-FY’2033)
- Recommendations from Analyst
1.1. Scope of the report1.2. Market segment analysis
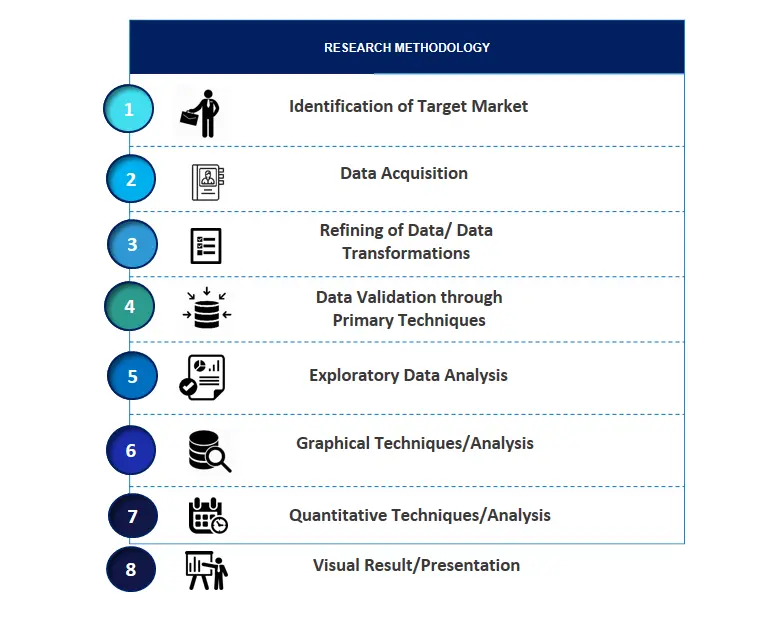
2.1. Research data source2.1.1. Secondary Data2.1.2. Primary Data2.1.3. SPER’s internal database2.1.4. Premium insight from KOL’s2.2. Market size estimation2.2.1. Top-down and Bottom-up approach2.3. Data triangulation
4.1. Driver, Restraint, Opportunity and Challenges analysis4.1.1. Drivers4.1.2. Restraints4.1.3. Opportunities4.1.4. Challenges4.2. COVID-19 Impacts of the China Cybersecurity Market
5.1. SWOT Analysis5.1.1. Strengths5.1.2. Weaknesses5.1.3. Opportunities5.1.4. Threats5.2. PESTEL Analysis5.2.1. Political Landscape5.2.2. Economic Landscape5.2.3. Social Landscape5.2.4. Technological Landscape5.2.5. Environmental Landscape5.2.6. Legal Landscape5.3. PORTER’s Five Forces5.3.1. Bargaining power of suppliers5.3.2. Bargaining power of buyers5.3.3. Threat of Substitute5.3.4. Threat of new entrant5.3.5. Competitive rivalry5.4. Heat Map Analysis
6.1. China Cybersecurity Market Manufacturing Base Distribution, Sales Area, Product Type6.2. Mergers & Acquisitions, Partnerships, Product Launch, and Collaboration in China Cybersecurity Market
7.1. China Cybersecurity Market Value Share and Forecast, By Offering, 2024-20337.2. Security Type7.2.1. Cloud Security7.2.2. Data Security7.2.3. Identity Access Management\7.2.4. Network Security7.2.5. Consumer Security7.2.6. Infrastructure Protection7.2.7. Others7.3. Services
8.1. China Cybersecurity Market Value Share and Forecast, By Deployment, 2024-20338.2. Cloud8.3. On-premise
9.1. China Cybersecurity Market Value Share and Forecast, By End User, 2024-20339.2. BFSI9.3. Healthcare9.4. Manufacturing9.5. Government & Defence9.6. IT and Telecommunication9.7. Others
10.1. China Cybersecurity Market Size and Market Share
11.1. China Cybersecurity Market Size and Market Share By Offering (2020-2026)11.2. China Cybersecurity Market Size and Market Share By Offering (2027-2033)
12.1. China Cybersecurity Market Size and Market Share By Deployment (2020-2026)12.2. China Cybersecurity Market Size and Market Share By Deployment (2027-2033)
13.1. China Cybersecurity Market Size and Market Share By End User (2020-2026)13.2. China Cybersecurity Market Size and Market Share By End User (2027-2033)
14.1. China Cybersecurity Market Size and Market Share By Region (2020-2026)14.2. China Cybersecurity Market Size and Market Share By Region (2027-2033)14.3. Eastern Region14.4. Western Region14.5. Northern Region14.6. Southern Region
15.1. Beijing Chaitin Future Technology Co.,Ltd15.1.1. Company details15.1.2. Financial outlook15.1.3. Product summary15.1.4. Recent developments15.2. CoreShield Times15.2.1. Company details15.2.2. Financial outlook15.2.3. Product summary15.2.4. Recent developments15.3. IBM Corporation15.3.1. Company details15.3.2. Financial outlook15.3.3. Product summary15.3.4. Recent developments15.4. IDsManager15.4.1. Company details15.4.2. Financial outlook15.4.3. Product summary15.4.4. Recent developments15.5. iJiami15.5.1. Company details15.5.2. Financial outlook15.5.3. Product summary15.5.4. Recent developments15.6. Palo Alto Networks15.6.1. Company details15.6.2. Financial outlook15.6.3. Product summary15.6.4. Recent developments15.7. QI-ANXIN Technology Group Inc.15.7.1. Company details15.7.2. Financial outlook15.7.3. Product summary15.7.4. Recent developments15.8. River Security15.8.1. Company details15.8.2. Financial outlook15.8.3. Product summary15.8.4. Recent developments15.9. ThreatBook15.9.1. Company details15.9.2. Financial outlook15.9.3. Product summary15.9.4. Recent developments15.10. Sophos Ltd.15.10.1. Company details15.10.2. Financial outlook15.10.3. Product summary15.10.4. Recent developments15.11. Tophant Inc.15.11.1. Company details15.11.2. Financial outlook15.11.3. Product summary15.11.4. Recent developments15.12. Others
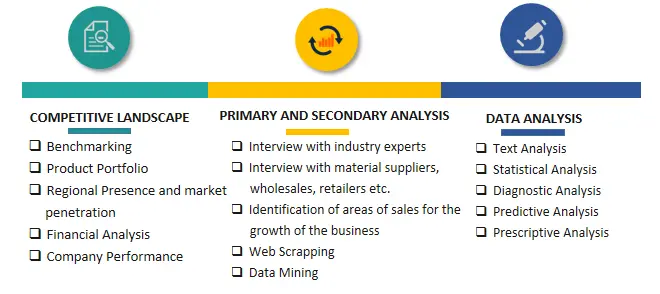
SPER Market Research’s methodology uses great emphasis on primary research to ensure that the market intelligence insights are up to date, reliable and accurate. Primary interviews are done with players involved in each phase of a supply chain to analyze the market forecasting. The secondary research method is used to help you fully understand how the future markets and the spending patterns look likes.
The report is based on in-depth qualitative and quantitative analysis of the Product Market. The quantitative analysis involves the application of various projection and sampling techniques. The qualitative analysis involves primary interviews, surveys, and vendor briefings. The data gathered as a result of these processes are validated through experts opinion. Our research methodology entails an ideal mixture of primary and secondary initiatives.

Frequently Asked Questions About This Report
PLACE AN ORDER
Year End Discount
Sample Report
Pre-Purchase Inquiry
NEED CUSTOMIZATION?
Request CustomizationCALL OR EMAIL US
100% Secure Payment






Related Reports
Our Global Clients
Our data-driven insights have influenced the strategy of 200+ reputed companies across the globe.